By early 2026, the DeFi space had lost over $77.1 billion to smart contract exploits and rug pulls since 2023. It’s not a matter of if your favorite protocol gets hacked-it’s when. And the attacks aren’t getting slower. They’re getting smarter.
How Smart Contracts Turn Into Money Magnets
Smart contracts are supposed to be trustless. They run on code, not people. But code isn’t perfect. In fact, the most dangerous flaws aren’t the flashy ones you see in movies. They’re quiet, boring, and often overlooked for years. Take the Truebit hack in January 2026. The contract had been live for nearly five years. No one found the integer overflow bug until a hacker used a fuzzing bot to test edge cases. Within minutes, they minted infinite TRU tokens and pulled out $26 million. The token price crashed to zero. Users who’d staked their life savings watched their balances vanish overnight. Logic bugs are now the #1 cause of DeFi losses, making up 26% of all exploits. That means the code doesn’t do what the developers thought it did. Maybe it allows someone to withdraw more than they deposited. Maybe it doesn’t check if a user actually owns the tokens they’re trying to swap. These aren’t bugs you’d catch in a quick code review. They hide in complex interactions between functions. Access control flaws are even more deadly. They caused 59% of all losses in 2025. That’s when a contract lets anyone-yes, anyone-do something only the owner should be able to do. Like changing the withdrawal limit, freezing funds, or even minting new tokens. Attackers don’t need to break encryption. They just need to find where the permission check is missing.The Rise of the Rug Pull
Rug pulls aren’t exploits. They’re thefts dressed up as innovation. A rug pull happens when developers build a project, attract users with big yields, then vanish. Sometimes they drain the liquidity pool. Other times, they change the contract to lock all funds and disappear. In 2025, 12.8% of all crypto thefts came from this exact pattern. And it’s getting easier. Many new DeFi projects launch with zero audits. Some don’t even lock their liquidity. They just deploy a contract, list it on a DEX, and start advertising on Twitter. Within days, they pull the plug. One project in late 2025 raised $42 million in just 72 hours. Three days later, the developers transferred all funds to a new wallet and shut down the website. The token dropped 99.9%. No one could withdraw. The worst part? Most users never realize they’re at risk until it’s too late. They see a 200% APY and assume it’s legit. They don’t check if the contract has been audited. They don’t look at who holds the admin key. They just click “approve” and “stake.”Why Ethereum and Solana Are the Biggest Targets
Ethereum and Solana account for 47% of all DeFi exploits. Why? Because they’re where the money is. Over 80% of DeFi TVL (Total Value Locked) sits on these chains. Attackers don’t waste time on small networks. They go where the wallets are full. But here’s the twist: 34% of attacks happened on contracts that were never audited. Another 38% slipped through audits because the auditors didn’t test the right scenarios. A contract can pass a standard audit and still be vulnerable to a flash loan attack or oracle manipulation. Take Cetus Protocol in February 2025. They used a single-price oracle to determine token values. Attackers flooded the market with fake tokens, skewed the price, then swapped their fake tokens for real ones. They walked away with $223 million. The contract was “audited.” The oracle wasn’t.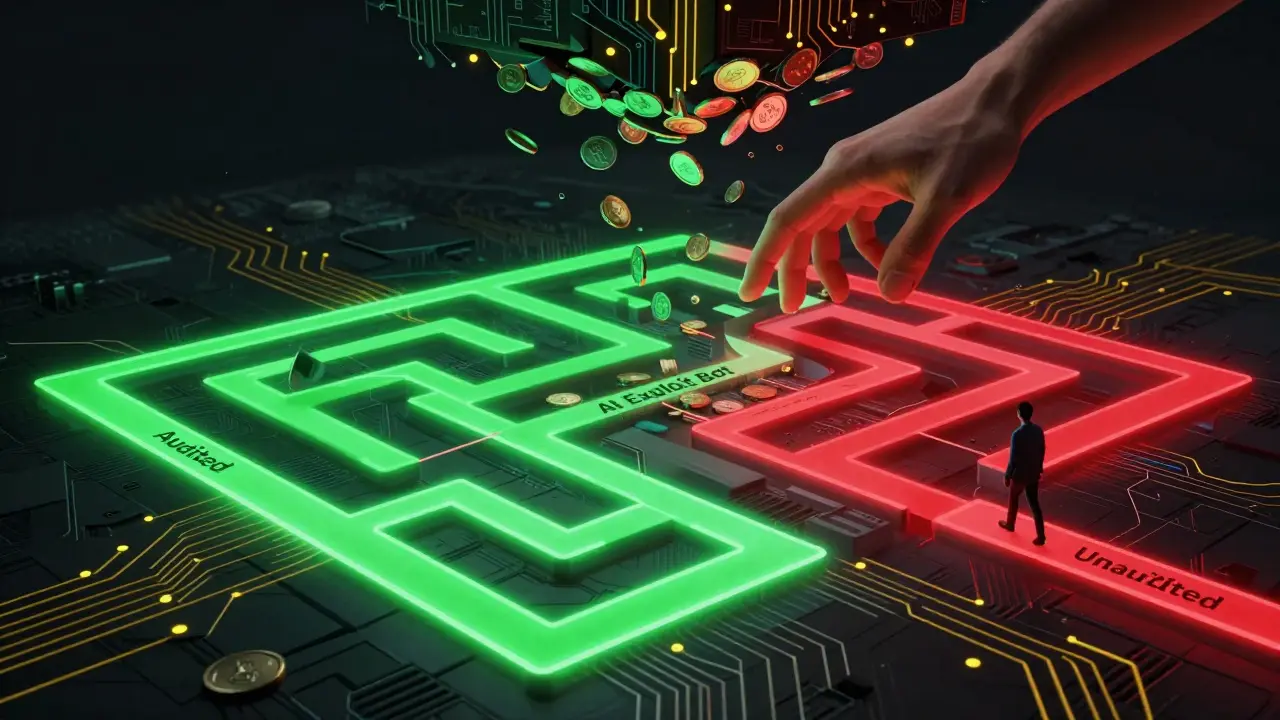
Legacy Contracts Are Sitting Ducks
Projects from 2020 to 2022 are getting picked apart. Ribbon Finance, Rari Capital, Yearn-they’ve all been hit multiple times in the last six months. Why? Because they’re old. Their code hasn’t changed. Their audits are outdated. And attackers are using AI tools to scan for forgotten vulnerabilities. A former Yearn security researcher, known as Storming0x, warned last year: “Attackers aren’t chasing new code. They’re hunting old code that’s been ignored.” That’s exactly what happened with Truebit. The bug had been there since day one. No one checked it again. Most protocols never re-audit. They assume “if it worked before, it’s fine.” But the threat landscape moves faster than that. New attack techniques emerge every month. What was safe in 2022 is a liability in 2026.What You Can Do to Protect Yourself
You can’t stop a hack. But you can stop yourself from getting burned.- Never give infinite token approvals. Many DeFi apps ask you to approve unlimited access to your tokens. That’s like giving someone your house key and saying, “Come back anytime.” Use tools like Etherscan to revoke approvals you don’t need.
- Check the audit status. If a project says “audited,” look up the audit report. Did they test for reentrancy? Flash loans? Oracle manipulation? If the report doesn’t mention those, the audit was shallow.
- Avoid high-yield traps. If a protocol offers 100%+ APY with no clear revenue model, it’s likely a rug pull. Real DeFi doesn’t need to pay you 200% to attract users.
- Withdraw from old contracts. If a project hasn’t updated its code or had a new audit in over a year, move your funds. Even if it’s still paying you, it’s a ticking bomb.
- Use hardware wallets. Never sign transactions from your phone or browser extension alone. A hardware wallet adds a physical layer of protection against phishing and malware.

The Bigger Picture: It’s Not Just Code
Here’s the truth most people miss: 80.5% of losses in 2024 came from off-chain attacks. That means phishing, fake websites, compromised private keys, and malicious browser extensions-not smart contract bugs. A user might have a perfectly secure wallet. But if they click a link that looks like MetaMask and enter their seed phrase, all the audits in the world won’t help. The biggest risk isn’t the code. It’s the person using it. Security firms like Halborn now recommend multi-sig wallets for protocols. That means at least three people must approve any withdrawal. No single person can steal the funds. It’s slow. It’s clunky. But it works. For users, the lesson is simple: assume every DeFi interaction is risky. Double-check everything. Question everything. And never trust a yield without understanding how it’s generated.What’s Next?
The industry is waking up. Formal verification is becoming more common. Adversarial simulations-where hackers simulate attacks before launch-are being adopted by top protocols. But these are expensive. Only the biggest players can afford them. For everyone else? Stay cautious. Stay skeptical. And remember: if something looks too good to be true, it probably is.What’s the difference between a smart contract exploit and a rug pull?
A smart contract exploit happens when a hacker finds a bug in the code-like a logic flaw or missing check-and uses it to steal funds. It’s technical. A rug pull is intentional fraud. The developers create a fake project, attract users, then drain the liquidity and disappear. No bug needed-just betrayal.
Can a smart contract be audited and still be hacked?
Yes. Audits are snapshots, not guarantees. They test known attack patterns, but new ones emerge daily. A contract audited in 2023 might be vulnerable to a 2026 attack vector. Also, many audits skip critical areas like oracle logic, flash loan interactions, or edge-case math. Even top firms miss things.
Are newer DeFi projects safer than older ones?
Not necessarily. New projects often skip audits to save time and money. Many have no multi-sig setup and centralized control. Older projects may have outdated code, but they’ve been tested under real conditions. The safest projects are those that regularly re-audit, use multi-sig, and have transparent governance-not just their age.
Why do so many hacks happen on Ethereum and Solana?
Because that’s where the money is. Over 80% of DeFi TVL is on these two chains. Attackers don’t waste time on small networks with $1 million locked. They target chains with billions. It’s simple economics: bigger target = bigger payout.
How can I check if a DeFi contract has been audited?
Look for a link to a public audit report on the project’s website or documentation. Then, search for the audit firm’s name (like Halborn, CertiK, or OpenZeppelin) and verify the report exists on their site. Check if the audit covers reentrancy, access control, and oracle manipulation. If the report is just a one-page summary, it’s not enough.
Is DeFi still worth using given these risks?
Yes-but only if you treat it like a high-risk investment, not a bank. Use small amounts. Avoid unknown protocols. Always verify contracts. And never invest more than you can afford to lose. DeFi offers real innovation, but it’s not safe by default. Your safety is your responsibility.


10 Responses
I swear, every time I see another DeFi project with 300% APY, I just close my tab. No one’s getting rich off ‘innovation’-they’re getting rich off your greed.
This is such a solid breakdown 🙌 I’ve been warning my friends about infinite approvals for months. Seriously, use Etherscan to revoke them-it’s like changing your locks after a roommate moves out. 💪
You say ‘audited’ like it means anything. Audits are a marketing tactic. Most firms use templates. They check for reentrancy and call it a day. What about oracle manipulation? Flash loan sandwich attacks? They don’t even test those. It’s theater. And you’re all falling for it.
Ethereum and Solana? Of course they’re targets. They’re the only chains with real liquidity. The rest are backwater ponds. You want safety? Move to Monero. Or better yet-don’t touch crypto at all. But if you’re dumb enough to stake your rent money on a contract written by some 19-year-old in a basement, don’t cry when it goes poof. You were warned.
The real issue isn’t the code. It’s the expectation that decentralized systems can be secure without centralized oversight. The moment you trust an algorithm over a person, you’ve already lost. And yet, here we are.
They’re all rigged. You think these audits are independent? Nah. CertiK’s got investors in half these projects. The whole thing’s a shell game. And the ‘official’ Twitter accounts? Fake. The devs are just laundering money through memes and influencer shilling.
While the technical analysis presented is accurate, one must consider the broader socio-economic context. In emerging markets, DeFi offers financial inclusion where traditional banking fails. The risks are real, but so is the opportunity. Prudence, not paranoia, should guide participation.
I appreciate the depth of this post. It's clear that the author has spent considerable time researching and understanding the nuances of DeFi vulnerabilities. I believe that education, not fear, is the key to navigating this space safely. Thank you for sharing such thoughtful insights.
wait so you’re telling me… the ‘unstoppable’ blockchain… is just… a bunch of janky scripts with a 1000% yield? 🤡 i mean… i get it. i really do. but why do i feel like i’m being scammed by a guy who says ‘trust me bro’ while holding a laptop in a dimly lit room? 🤔
i’ve been in crypto since 2017. i’ve lost money. i’ve made money. the one thing that’s always true? if you don’t understand how it works, don’t put money in. simple. i revoke approvals monthly. use a hw wallet. never trust a 200% apy. done.